Kindly fill up the following to try out our sandbox experience. We will get back to you at the earliest.
Essential Data Security Safeguards for Effective Data Management
Discover essential data security safeguards to protect sensitive information effectively.

Introduction
In an era where digital threats are ever-evolving, effective data management has become paramount for organizations navigating a complex landscape filled with potential risks. By implementing essential data security safeguards, organizations can protect sensitive information while enhancing operational efficiency and ensuring compliance with regulations. As technology evolves and cyber threats become more sophisticated, organizations must ensure their data security measures are robust and adaptable.
We will explore best practices for:
- Identifying sensitive data
- Classifying sensitive data
- Safeguarding sensitive data
While examining the vital role of advanced technologies in fortifying security protocols. Failure to implement robust data security measures can lead to significant operational and reputational damage.
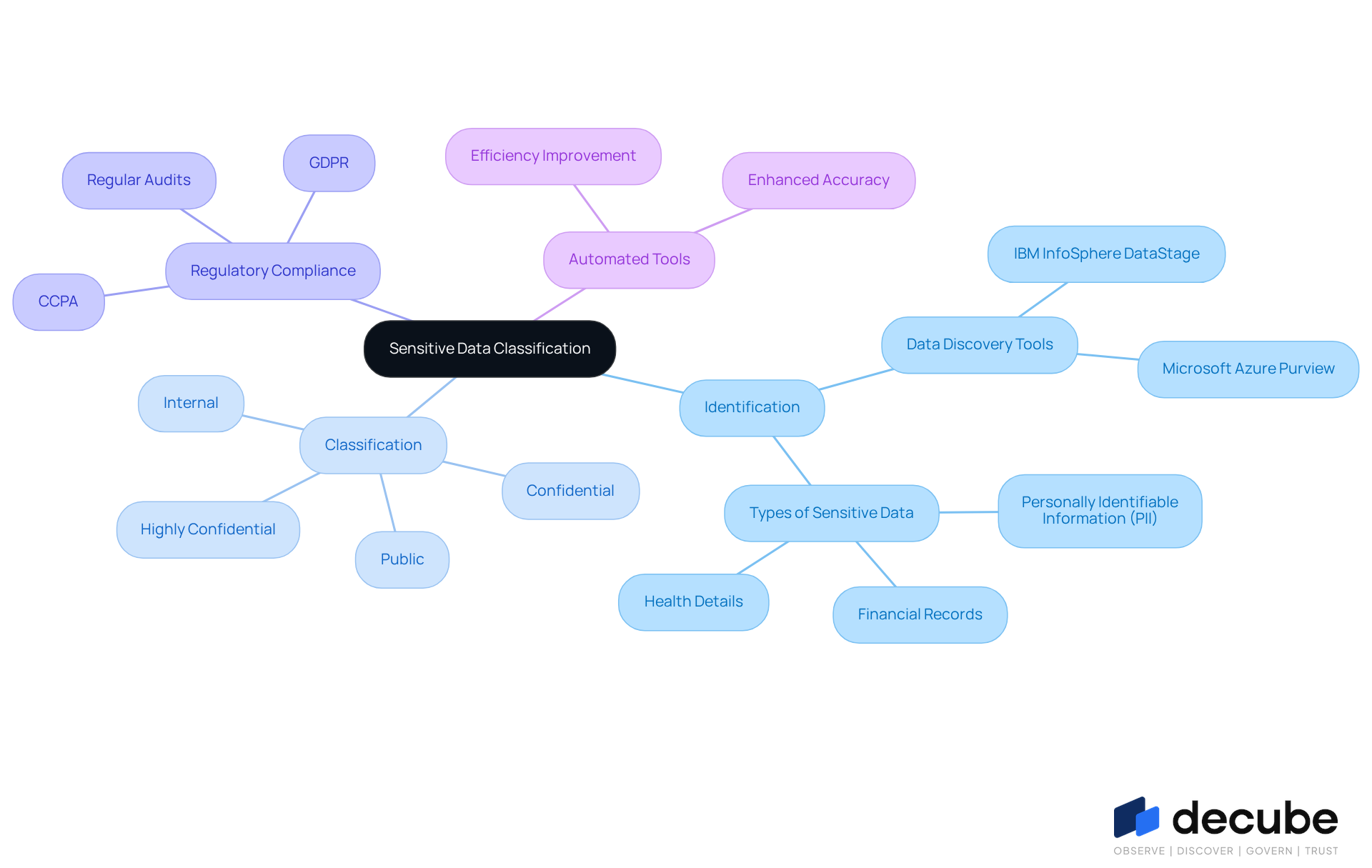
Identify and Classify Sensitive Data
The foundation of effective information security management lies in the precise identification and classification of sensitive information. Organizations should establish a thorough inventory of all information assets, encompassing both structured and unstructured types. The implementation of automated tools for information discovery and classification significantly enhances accuracy and efficiency, reducing reliance on manual processes. It is imperative that sensitive information, such as personally identifiable information (PII), financial records, and health details, is accurately tagged to facilitate proper handling.
Implementing a tiered classification system - such as Public, Internal, Confidential, and Highly Confidential - helps ascertain the level of protection needed for each type of information. Regular reviews and updates of classifications are essential to adapt to changes in information usage and evolving regulatory requirements. In 2026, a significant number of organizations are projected to adopt automated tools for information discovery and classification, indicating a rising trend towards improved information management practices. As highlighted by privacy specialists, effective categorization not only protects sensitive details but also aids adherence to regulations such as GDPR and CCPA, ultimately enhancing quality and organizational efficiency. This proactive approach not only safeguards sensitive information but also positions organizations to meet evolving regulatory demands effectively.
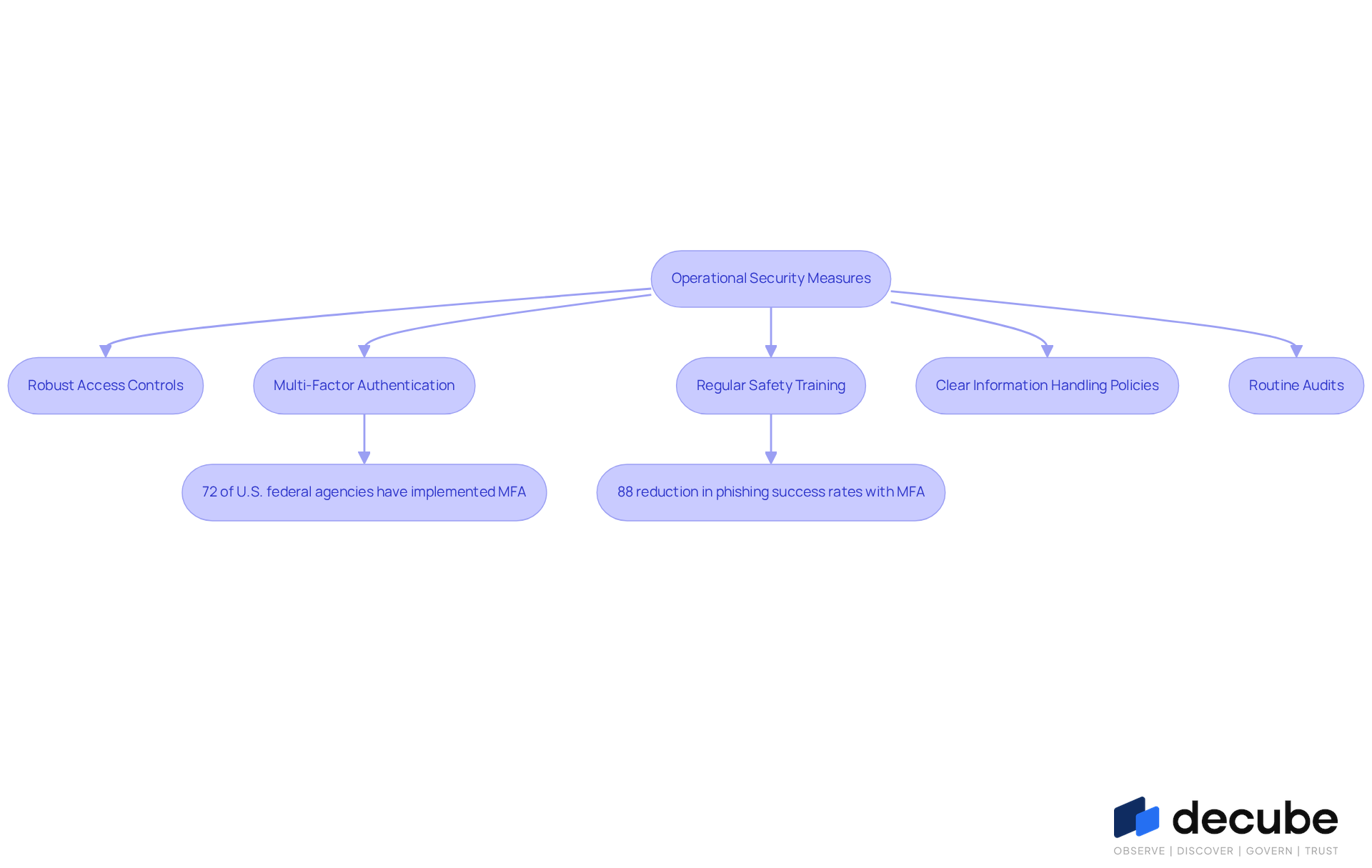
Establish Robust Operational Security Measures
To effectively safeguard sensitive information, organizations must adopt data security safeguards as part of their comprehensive operational security measures. Robust access controls are vital, ensuring that only authorized personnel can access crucial data. Decube's automated crawling feature enhances metadata management by automatically refreshing information when sources are connected. This reduces the need for manual updates and helps maintain accurate and up-to-date information. Multi-factor authentication (MFA) acts as a crucial extra layer of protection, with the market expected to reach $40 billion by 2030, demonstrating its critical role in data protection. Present adoption rates show that although 72% of U.S. federal agencies have implemented MFA, only 31% of cloud service users have it activated. This gap highlights the challenges organizations face in implementing comprehensive data security safeguards. Furthermore, 28% of users who have activated MFA are still targeted by attackers, underscoring the need for continuous improvement in security protocols.
Regular safety training for employees is crucial for organizations to provide, raising awareness about threats such as phishing and social engineering. Notably, 88% of companies that adopted MFA reported a reduction in phishing success rates. Creating clear information handling policies and incident response strategies is essential for prompt action in the event of a breach. Moreover, performing routine audits and vulnerability evaluations is necessary to recognize and address weaknesses, as entities typically take 74.3 days to resolve critical application vulnerabilities, leaving information exposed during this time. By prioritizing these strategies, organizations can significantly mitigate risks and enhance their overall security posture with effective data security safeguards.
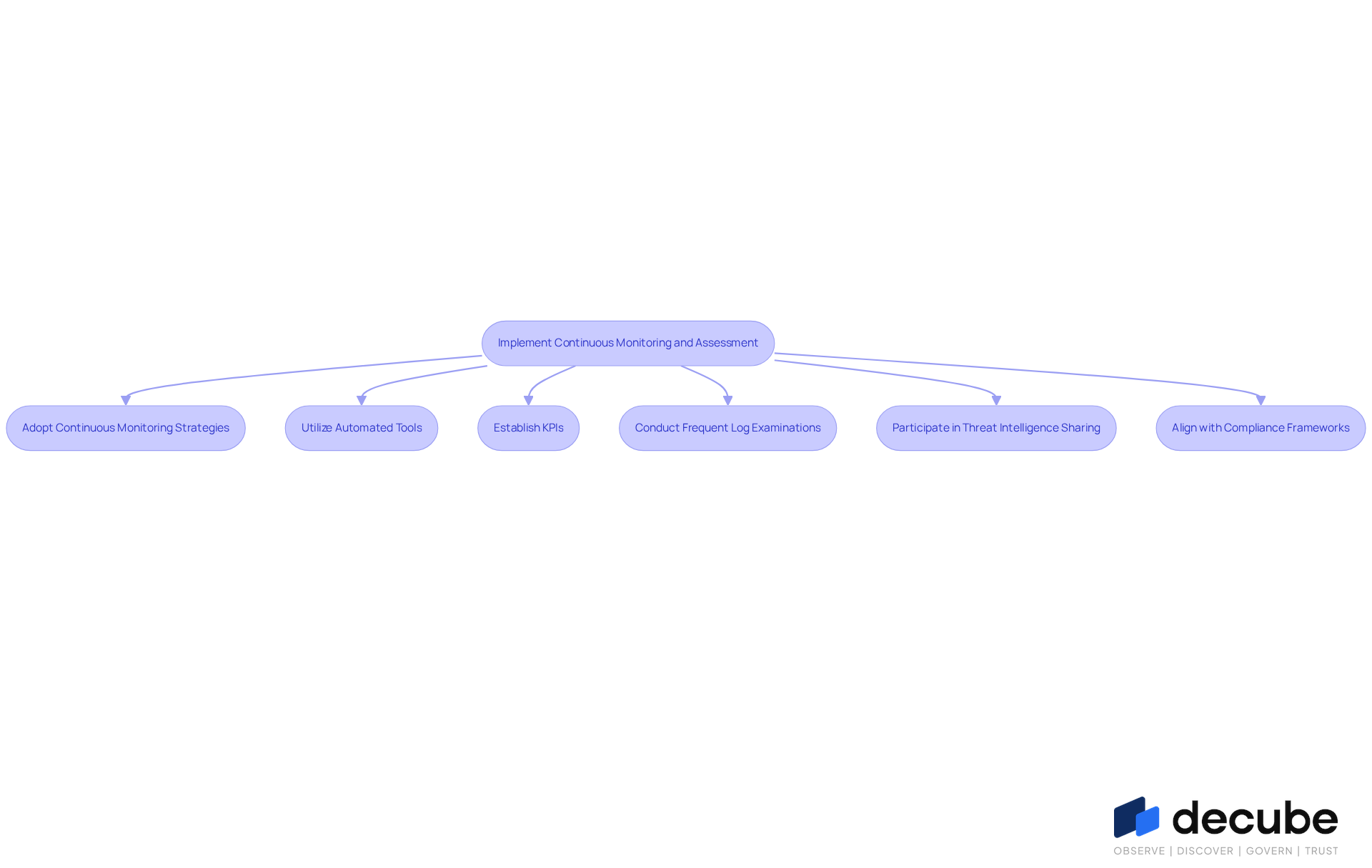
Implement Continuous Monitoring and Assessment
Organizations face increasing challenges in maintaining robust data security safeguards amidst evolving threats. To address these challenges, they must adopt continuous monitoring and evaluation strategies that incorporate data security safeguards. This includes utilizing automated tools, such as Decube's Data Trust Platform, which enables real-time observation of access and usage patterns. These tools can be integrated into platforms like Jira, Slack, or ServiceNow, enhancing data observability and governance through effortless metadata management and secure access control.
Establishing key performance indicators (KPIs) is crucial for evaluating the effectiveness of data security safeguards. Research indicates that organizations improving breach detection can save around $1.8 million per incident. Frequent examinations of logs and alerts are essential for identifying unusual activities that may indicate a breach. Additionally, regular risk evaluations allow companies to assess their data security safeguards and adjust strategies accordingly.
Participating in threat intelligence sharing with industry colleagues further increases awareness of emerging dangers, fostering a proactive protective environment. Case studies, including examples from the 'Communication Crisis at Shai-Hulud' and 'Continuous Compliance Automation,' demonstrate that organizations adopting these practices have experienced significant enhancements in their incident response times and overall effectiveness. Furthermore, two-thirds of providers support frameworks like CMMC 2.0, HIPAA, and NIST 800-171, highlighting the relevance of continuous monitoring in compliance efforts.
Ultimately, the integration of continuous monitoring not only fortifies security but also aligns with compliance mandates, ensuring organizations are well-prepared for future challenges.
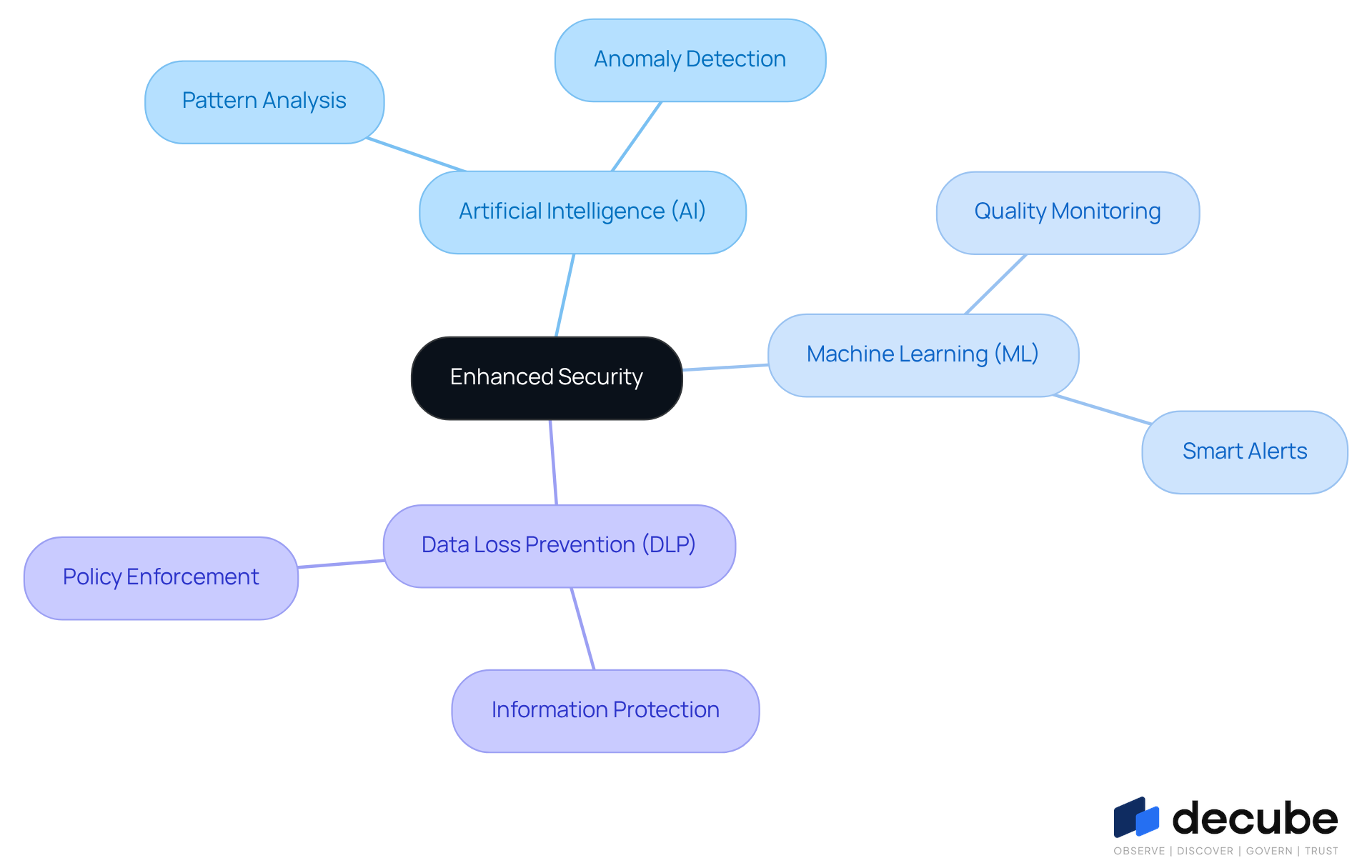
Leverage Advanced Technologies for Enhanced Security
To enhance data security safeguards, organizations must leverage advanced technologies such as artificial intelligence (AI) and machine learning (ML). These technologies play a crucial role in analyzing extensive datasets to identify patterns and detect anomalies that may indicate security threats. Organizations often struggle to manage sensitive information effectively, leading to potential data breaches. Implementing data security safeguards, including information loss prevention (DLP) solutions, is vital for monitoring and controlling transfers, thereby ensuring that sensitive details are not improperly shared. By 2026, modern DLP technologies will utilize machine learning and behavioral analytics to enhance detection capabilities and minimize false positives, leading to a more efficient user experience.
Decube exemplifies this approach through its advanced quality monitoring features, which enhance data integrity and streamline oversight. Its ML-powered tests automatically identify thresholds for quality, ensuring that entities can uphold high standards of integrity. Additionally, Decube's smart alerts group notifications to prevent overwhelming users, allowing for timely responses to potential issues. The platform's automated crawling feature further enhances information observability by ensuring that metadata is effortlessly managed and kept current, which is crucial for effective governance.
Encryption technologies should also be utilized to protect information both at rest and in transit, aligning with the need for quantum-ready encryption as entities prepare for future threats. Frequent updates to protection software and systems are vital to guard against new vulnerabilities and threats. By incorporating these advanced technologies and ensuring ongoing oversight, companies can create a strong protective structure that includes data security safeguards, thus reducing risks and improving overall information management practices.
Case studies demonstrate the effectiveness of DLP solutions in practical scenarios, highlighting how companies have successfully diminished security incidents through proactive measures. For example, the implementation of next-generation DLP has allowed companies to categorize essential information precisely and enforce policies efficiently, resulting in considerable advancements in information protection. As organizations continue to adapt to the evolving cybersecurity landscape, the strategic use of AI, ML, and DLP technologies, alongside Decube's comprehensive data trust platform, will be vital in fortifying their defenses against increasingly sophisticated threats.
Conclusion
In an era where data breaches are increasingly common, organizations face mounting pressure to implement effective data management strategies. Effective data management relies on implementing key data security safeguards that protect sensitive information from emerging threats. Organizations must focus on:
- Identifying and classifying data accurately
- Establishing robust operational security measures
- Leveraging advanced technologies to enhance their defenses
This approach not only protects critical assets but also ensures adherence to regulatory standards governing data protection.
Throughout the article, key strategies such as:
- The tiered classification of sensitive data
- Robust access controls
- Multi-factor authentication
- Continuous monitoring
have been discussed as vital components of a comprehensive data security framework. The integration of advanced technologies, including AI and machine learning, further strengthens these measures by enabling real-time analysis and anomaly detection. Ongoing training and regular audits are crucial for maintaining a proactive security posture and adapting to the constantly evolving landscape of cyber threats.
In conclusion, organizations must recognize that effective data management is not solely about compliance but also about fostering a culture of security awareness and resilience. By prioritizing these best practices and embracing innovative technologies, businesses can significantly mitigate risks and enhance their overall security posture. Ultimately, the commitment to robust data management practices will define an organization's resilience in the face of evolving cyber threats.
Frequently Asked Questions
Why is identifying and classifying sensitive data important for organizations?
Identifying and classifying sensitive data is crucial for effective information security management, as it helps organizations understand their information assets and ensures proper handling of sensitive information.
What types of sensitive information should organizations focus on?
Organizations should focus on sensitive information such as personally identifiable information (PII), financial records, and health details.
How can organizations enhance the accuracy and efficiency of data classification?
Organizations can enhance accuracy and efficiency by implementing automated tools for information discovery and classification, reducing reliance on manual processes.
What is a tiered classification system, and what levels does it typically include?
A tiered classification system categorizes information based on its sensitivity and required protection level. Typical levels include Public, Internal, Confidential, and Highly Confidential.
Why are regular reviews and updates of data classifications necessary?
Regular reviews and updates are necessary to adapt to changes in information usage and evolving regulatory requirements, ensuring that classifications remain relevant and effective.
What trend is expected in 2026 regarding the adoption of data classification tools?
By 2026, a significant number of organizations are projected to adopt automated tools for information discovery and classification, indicating a trend towards improved information management practices.
How does effective categorization of sensitive data aid in regulatory compliance?
Effective categorization helps organizations adhere to regulations such as GDPR and CCPA, ensuring that sensitive information is protected and organizational practices are aligned with legal requirements.
What are the benefits of a proactive approach to data classification?
A proactive approach to data classification safeguards sensitive information and positions organizations to meet evolving regulatory demands effectively, ultimately enhancing quality and organizational efficiency.
List of Sources
- Identify and Classify Sensitive Data
- Quotes Related to Data and Data Governance (https://blog.idatainc.com/quotes-related-to-data-and-data-governance)
- Top 7 Data Classification Best Practices for Businesses | archTIS (https://spirion.com/blog/7-data-classification-best-practices)
- Data Classification Best Practices: Strategies & Compliance (https://fortra.com/blog/data-classification-best-practices-strategies-compliance)
- How can you identify and classify sensitive data in your Data Governance framework? (https://linkedin.com/advice/3/how-can-you-identify-classify-sensitive-data-your)
- Establish Robust Operational Security Measures
- Top 10 Data Security Trends for 2026 (https://cyberhaven.com/blog/ten-data-security-trends-for-2026)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)
- Why Data Protection Must Be a Strategic Priority in 2026 (https://edgescan.com/why-data-protection-must-be-a-strategic-priority-in-2026)
- Multi-Factor Authentication Adoption Rates: Are We Doing Enough? (https://patentpc.com/blog/multi-factor-authentication-adoption-rates-are-we-doing-enough)
- Data Protection Strategies for 2026 (https://hyperproof.io/resource/data-protection-strategies-for-2026)
- Implement Continuous Monitoring and Assessment
- Top Cybersecurity Metrics and KPIs for 2026 | UpGuard (https://upguard.com/blog/cybersecurity-metrics)
- Continuous Monitoring in 2026: Best Practices for Regulated Industries (https://telos.com/blog/2026/04/14/continuous-monitoring-in-highly-regulated-industries-best-practices)
- Continuous Compliance Monitoring: 2026 Technical Guide (https://apptega.com/blog/continuous-monitoring)
- What Are the Key Cybersecurity KPIs in 2026 and How to Track Them Effectively? (https://linkedin.com/pulse/what-key-cybersecurity-kpis-2026-how-track-them-effectively-0ilaf)
- Leverage Advanced Technologies for Enhanced Security
- 9 AI Cybersecurity Trends to Watch in 2026 (https://sentinelone.com/cybersecurity-101/data-and-ai/ai-cybersecurity-trends)
- Data Protection Strategies for 2026 (https://hyperproof.io/resource/data-protection-strategies-for-2026)
- State of AI Cybersecurity in 2026: What the Data Tells Us About What's Coming Next (https://kiteworks.com/cybersecurity-risk-management/ai-cybersecurity-2026-trends-report)

_For%20light%20backgrounds.svg)
















