Kindly fill up the following to try out our sandbox experience. We will get back to you at the earliest.
4 Best Practices for Enhancing Company Data Security
Enhance your company data security with best practices for identifying, protecting, and monitoring sensitive information.

Introduction
In an era where data breaches are increasingly prevalent, organizations face mounting pressure to protect sensitive information effectively. As cyber threats evolve, implementing best practices for data security safeguards valuable assets and ensures compliance with regulatory standards. Despite the increasing awareness of data security, many organizations find themselves ill-equipped to handle the complexities of data classification and protection. This oversight not only jeopardizes sensitive information but also exposes organizations to potential legal and financial penalties.
What strategies can organizations adopt to enhance their data security and foster a culture of awareness and compliance?
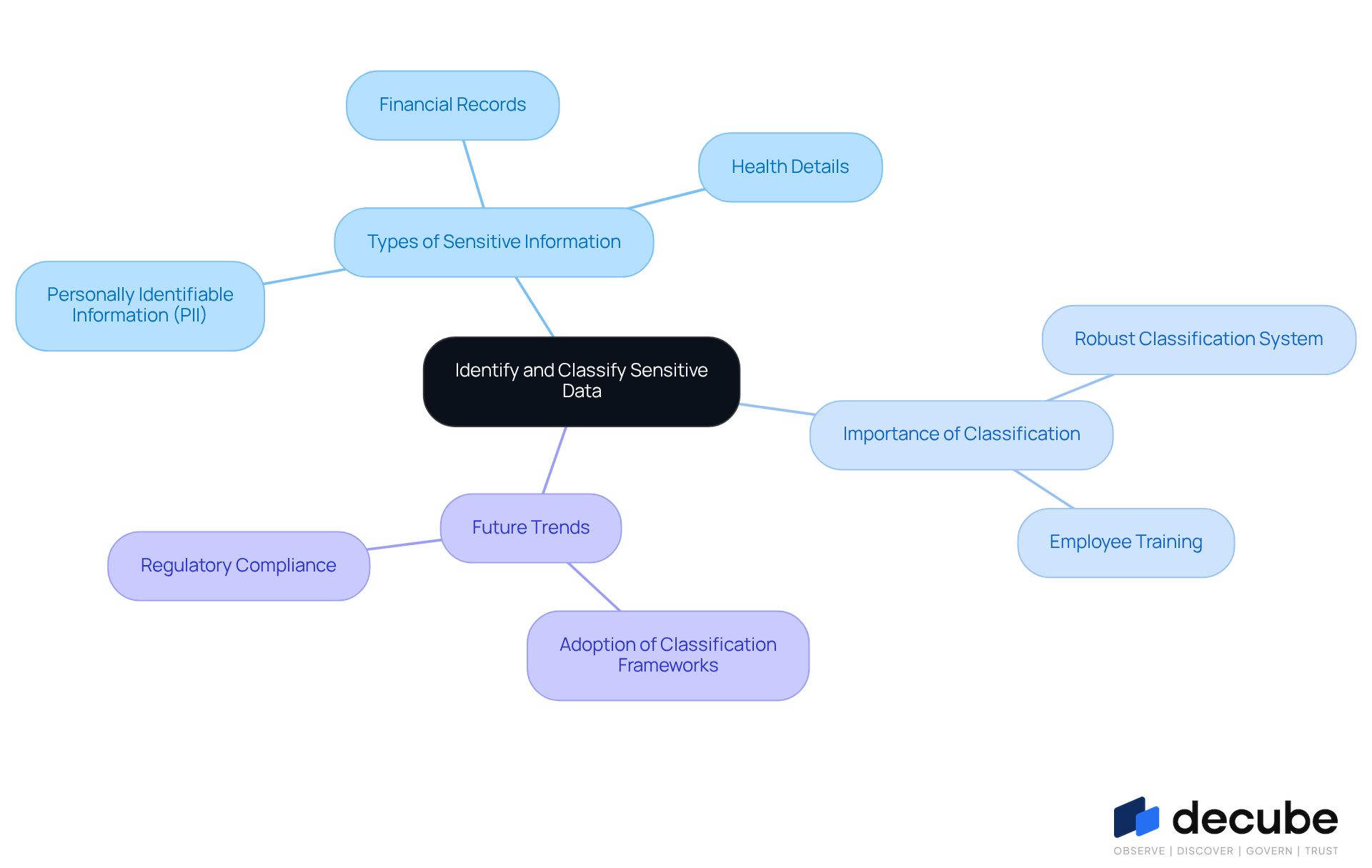
Identify and Classify Sensitive Data
Organizations face increasing pressure to effectively identify and classify sensitive information to safeguard against data breaches. This process requires cataloging information assets and evaluating their sensitivity according to specific characteristics and regulatory requirements. Sensitive information typically includes:
- Personally identifiable information (PII)
- Financial records
- Health details
A robust classification system is essential for effectively prioritizing information protection efforts. For instance, automated tools can greatly simplify the identification process, ensuring that sensitive information is precisely labeled and consistently monitored. By 2026, approximately 70% of organizations are expected to adopt classification frameworks, highlighting the growing recognition of their importance in enhancing security posture. Regular training sessions for employees on information sensitivity further reinforce the importance of these classification efforts, fostering a culture of awareness and compliance within the organization. Without a robust classification system, organizations may expose themselves to significant security risks and regulatory penalties.
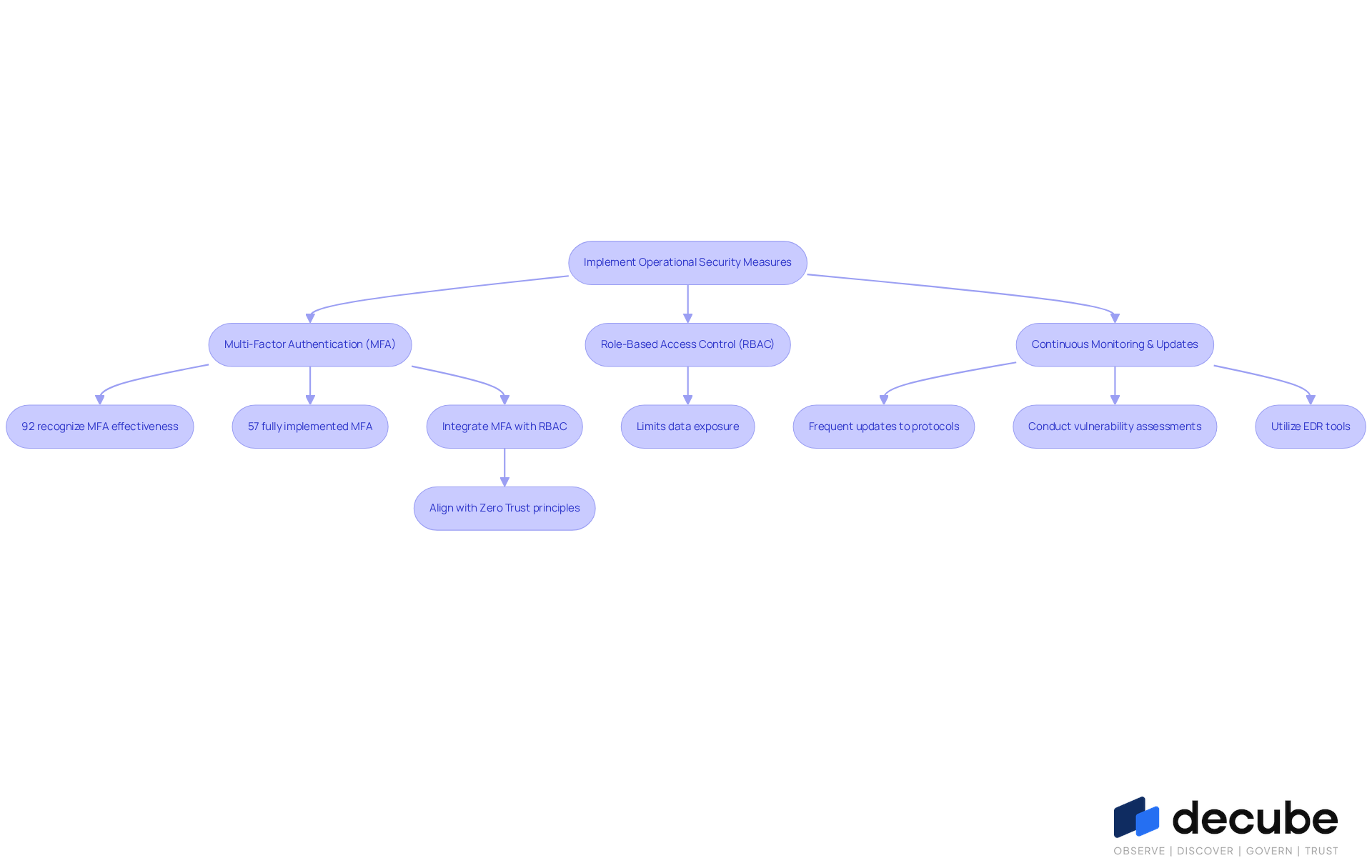
Implement Operational Security Measures
To protect confidential information effectively, organizations must establish robust operational safeguards. Multi-factor authentication (MFA) serves as a crucial layer of security, ensuring that only authorized personnel can access critical information. Research indicates that while 92% of organizations recognize the effectiveness of MFA in safeguarding sensitive information, only 57% have fully implemented it across all access points. This discrepancy highlights the urgent need for organizations to prioritize the adoption of MFA, particularly in high-risk areas such as email and financial tools.
In addition to MFA, employing role-based access control (RBAC) can significantly limit data exposure by restricting access based on user roles. This minimizes the risk of unauthorized access to sensitive information. Frequent updates to protective protocols and conducting vulnerability assessments are crucial practices for identifying and addressing potential weaknesses within the system. For example, entities can utilize endpoint detection and response (EDR) tools to observe and react to suspicious activities in real-time, thus improving their overall safety stance.
Furthermore, integrating MFA with RBAC not only enhances protection but also aligns with the principles of Zero Trust, ensuring that access is granted based on verified identity and necessity. As cyber threats continue to evolve, entities must remain vigilant and proactive in their security strategies to mitigate risks effectively. With Decube's automated crawling capability, companies can further improve their information governance by automatically refreshing metadata once sources are linked, removing the requirement for manual updates. This feature simplifies metadata management and gives organizations the ability to control who can view or edit information through a clear approval process. Without proactive measures, organizations risk significant exposure to cyber threats that could compromise their sensitive data.
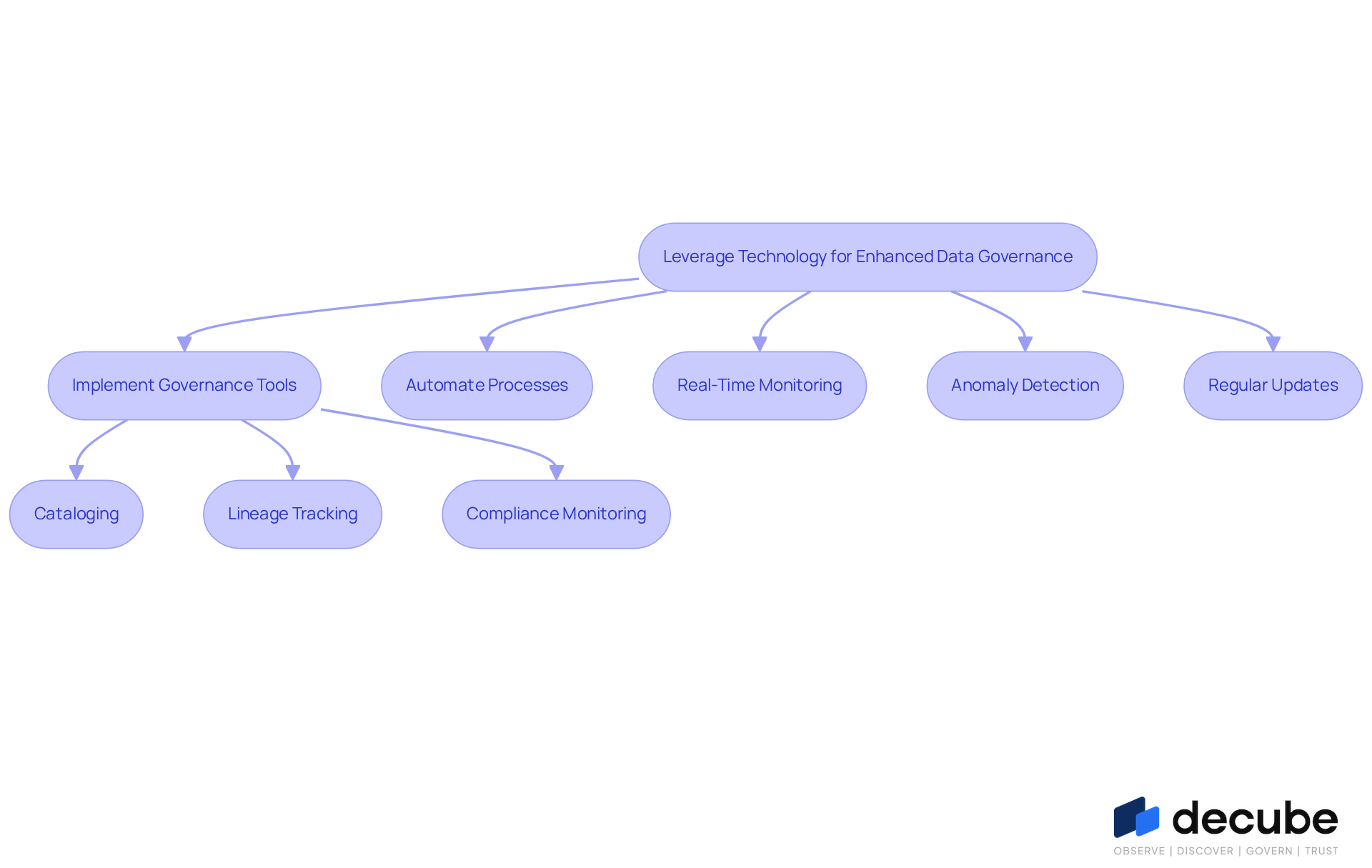
Leverage Technology for Enhanced Data Governance
To enhance information security, organizations must leverage advanced technology to strengthen their governance frameworks. Implementing robust information governance tools, such as Decube, can automate critical processes like cataloging, lineage tracking, and compliance monitoring. Decube provides features for real-time monitoring of information pipelines and automated policy management, ensuring that governance is both efficient and effective. Its automated crawling feature removes the need for manual metadata updates, significantly enhancing visibility and governance through streamlined management processes. Decube's intuitive design enhances clarity in information pipelines, fostering improved collaboration among teams.
By employing machine learning algorithms for anomaly detection, organizations can proactively identify potential security threats, thereby significantly mitigating risks. Regular updates to these technologies, along with seamless integration into existing systems, are essential for keeping pace with evolving compliance requirements. Efficient governance has been demonstrated to result in a 37% decrease in breach risks, highlighting the necessity of these tools in today’s information-driven environment. Ultimately, the integration of Decube not only streamlines governance processes but also fortifies the organization's overall security posture.
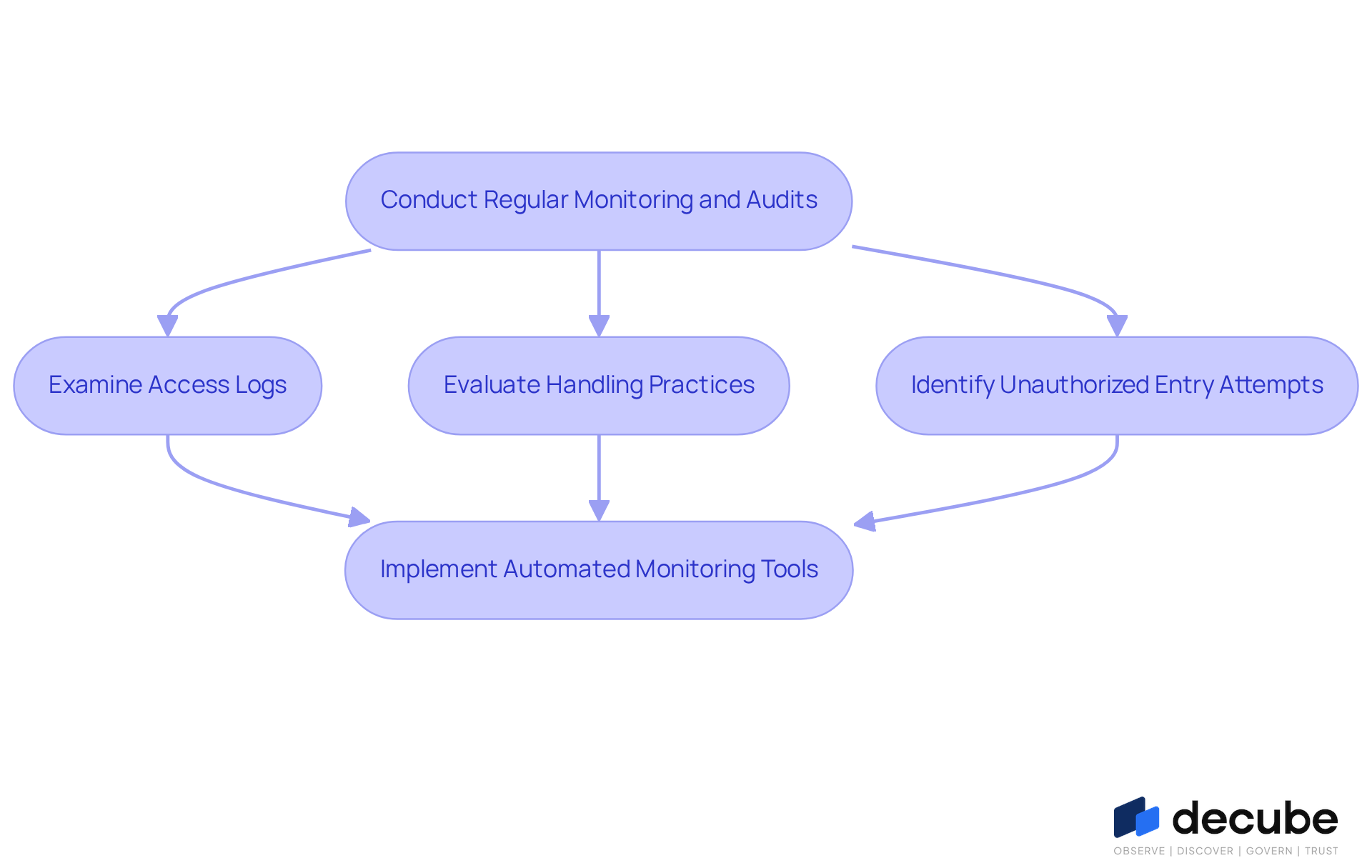
Conduct Regular Monitoring and Audits
Establishing a robust information protection strategy requires regular oversight and evaluations to ensure effectiveness. Organizations should implement a routine for conducting security audits to assess the efficacy of their information protection measures. This process involves:
- Examining access logs
- Evaluating handling practices
- Identifying unauthorized entry attempts
Automated monitoring tools are essential for ongoing oversight, helping organizations quickly identify anomalies and respond effectively. For instance, quarterly audits can ensure compliance with regulations such as SOC 2 and GDPR while pinpointing areas for enhancement in data protection practices. Ultimately, neglecting regular security audits can leave organizations vulnerable to significant data breaches and compliance failures.
Conclusion
Organizations often struggle to keep pace with the rapidly changing cyber threat landscape. Implementing effective data security practices is essential for organizations aiming to safeguard sensitive information against these evolving threats. Companies can significantly enhance their security posture by:
- Identifying and classifying sensitive data
- Establishing robust operational security measures
- Leveraging advanced technology for data governance
- Conducting regular monitoring and audits
Key strategies discussed include the implementation of multi-factor authentication and role-based access control, which serve as critical layers of protection. Additionally, utilizing automated governance tools like Decube can streamline compliance and monitoring processes, while regular security audits ensure that organizations remain vigilant and proactive in their security efforts. Implementing these practices not only mitigates risks but also cultivates a culture of security awareness among employees.
A comprehensive approach to data security is essential for organizations. They are encouraged to adopt these best practices to create a resilient framework that not only protects sensitive information but also builds trust with clients and stakeholders. By neglecting data security, organizations risk not only their sensitive information but also their reputation and client trust.
Frequently Asked Questions
Why is it important for organizations to identify and classify sensitive data?
Organizations need to identify and classify sensitive data to safeguard against data breaches and meet regulatory requirements. This process helps in cataloging information assets and evaluating their sensitivity.
What types of information are typically classified as sensitive?
Sensitive information typically includes personally identifiable information (PII), financial records, and health details.
How can organizations improve their sensitive data classification efforts?
Organizations can improve their classification efforts by implementing a robust classification system, utilizing automated tools for identifying sensitive information, and ensuring consistent monitoring and labeling.
What is the expected trend regarding the adoption of classification frameworks by 2026?
By 2026, approximately 70% of organizations are expected to adopt classification frameworks, indicating a growing recognition of their importance in enhancing security posture.
How can employee training contribute to the classification of sensitive data?
Regular training sessions for employees on information sensitivity reinforce the importance of classification efforts and help foster a culture of awareness and compliance within the organization.
What are the risks of not having a robust classification system in place?
Without a robust classification system, organizations may expose themselves to significant security risks and regulatory penalties.
List of Sources
- Identify and Classify Sensitive Data
- Data Privacy in 2026: What Every Business Leader Needs to Know | Vantage Point (https://vantagepoint.io/blog/sf/blog/insights/data-privacy-2026-business-leaders-guide)
- 4 Types of Sensitive Data You Should Protect in 2026 (https://redactable.com/blog/types-of-sensitive-data-to-know-and-protect)
- Data Classification Practices: SP 1800-39 ipd | CSRC (https://csrc.nist.gov/News/2026/sp-1800-39-ipd-data-classification-practices)
- 19 Inspirational Quotes About Data | The Pipeline | ZoomInfo (https://pipeline.zoominfo.com/operations/19-inspirational-quotes-about-data)
- Implement Operational Security Measures
- The Silent Cyberattack Bypassing MFA: What Every CEO Must Know In 2026 (https://forbes.com/councils/forbestechcouncil/2026/02/23/the-silent-cyberattack-bypassing-mfa-what-every-ceo-must-know-in-2026)
- Multi-Factor Authentication Adoption Rates: Are We Doing Enough? (https://patentpc.com/blog/multi-factor-authentication-adoption-rates-are-we-doing-enough)
- Top 10 Multifactor Authentication Solutions for 2026 (https://secureitworld.com/article/top-10-multifactor-authentication-solutions-to-prevent-unauthorized-access)
- Cyber Essentials 2026: Mandatory MFA on ALL cloud services (https://pushsecurity.com/blog/cyber-essentials-april-2026-update)
- 8 best practices for efficient MFA in 2026 (https://blog.scalefusion.com/mfa-best-practices)
- Leverage Technology for Enhanced Data Governance
- Top 9 AI-Powered Data Governance Tools for 2026 (https://kiteworks.com/cybersecurity-risk-management/ai-data-governance-tools-2026)
- Data Governance Market Report 2026 - Research and Markets (https://researchandmarkets.com/reports/5767497/data-governance-market-report?srsltid=AfmBOooo7jQKr1lOl2ps-exroZSrr9LgA2S1T_pBzMrnxXm7-g5C1Ewq)
- Data Governance Statistics | 2026 Edition – Gitnux (https://gitnux.org/data-governance-statistics)
- Top Data Governance Tools for Smarter Compliance in 2026 (https://usercentrics.com/knowledge-hub/data-governance-tools)
- Global Data Governance Market Expected to Reach USD 19.9 Billion by 2034 - IMARC Group (https://imarcgroup.com/data-governance-market-statistics)
- Conduct Regular Monitoring and Audits
- January 2026 OCR Cybersecurity Newsletter (https://hhs.gov/hipaa/for-professionals/security/guidance/cybersecurity-newsletter-january-2026)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Cyber security compliance statistics for 2026 | CyberArrow (https://cyberarrow.io/blog/cyber-security-compliance-statistics)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)

_For%20light%20backgrounds.svg)